CECoE
Converged Edge Center of Excellence (CECoE)
Put intelligence where work happens—reliable, governed, and cost-effective.
Executive Summary
The Converged Edge CoE is a practitioner-led forum for designing, deploying, and operating edge platforms that run real workloads—safely and at scale. We focus on the “last mile of compute” across factories, buildings and campuses, utilities, retail, logistics, healthcare facilities, and remote/harsh sites. The CoE publishes reference architectures, playbooks, evaluation suites, and audit-ready evidence so organizations can run data collection, control, analytics/AI, and integrations at or near the source—online or offline—while keeping governance, security, and cost under control.
Who We Serve
- OT/IT & Platform Teams: edge architects, site reliability engineers, network engineers, infra/platform owners.
- Operations: plant and facilities leaders, utilities field ops, retail/logistics site ops, hospital facilities/clinical engineering.
- Data/AI & Applications: ML/AI teams, app developers, vision/analytics owners, product platform managers.
- Security & Compliance: CISOs, product security, risk/audit leaders.
- Leadership: CIO/CTO/COO, heads of digital/industry programs.
- Partners: hardware vendors, integrators/SIs, telecom/MEC providers, standards bodies, academia.
How We Succeed?
By establishing an eco-system of self-sustaining collaboration between end-uses, academia and solution providers that encourage:
- Knowledge sharing of roadmaps, technology and approaches toward the transformative future
- Build an annual agenda of focus topics and experts who can inspire the vision for the transformation through virtual and live interactive sessions
- Interactions within the manufacturing eco-system, share ideas and approaches
- Provide relevant content in a consumable form and expand awareness of challenges, solutions and outcomes
Charter & Objectives
- Reliability at the Edge: deterministic behavior, graceful degradation offline, quick recovery after faults.
- Operational Simplicity: zero-touch provisioning, safe updates, small-footprint orchestration, repeatable runbooks.
- Performance & Cost: right-sized compute/accelerators, local processing to reduce latency and backhaul, predictable TCO.
- Security & Governance: identity/attestation, policy gates, RBAC, audit trails, and safe rollback built-in.
- Interoperability: open interfaces from device to platform to enterprise; avoid lock-in via pragmatic standards.
- Scalability: patterns that work from a single site to thousands, with minimal on-site expertise.
Focus Pillars
- Edge Platform Architecture & Orchestration
– What: footprint-appropriate orchestration (lightweight K8s, containers, WASM, micro-VMs), image signing, registries, and staging/canary/rollback.
– Why: the difference between one-off pilots and fleet-scale operations is packaging and lifecycle.
– Starter outcomes: opinionated repo structures, image policies, blue/green and canary patterns, remote shell/exec guardrails. - Connectivity & Network Slices
– What: deterministic and best-effort paths (wired, Wi-Fi/6/7, private 5G/LTE), VLAN/VRF/SD-WAN, TSN where needed, egress shaping.
– Why: control loops and high-rate video/telemetry need consistent latency and isolation.
– Starter outcomes: reference topologies per site class; QoS maps tied to SLAs; inline enforcement and observability taps. - Data Plane & Storage at the Edge
– What: streaming ingestion, local time-series/event stores, object caches, compaction, and sync to central lakes.
– Why: keep critical data close for low latency and resilience; ship the minimum upstream.
– Starter outcomes: retention policies, conflict handling, back-pressure, bandwidth caps, and “evidence first” logging. - Resilience, HA/DR & Offline-First
– What: node/zone redundancy, watchdogs, UPS awareness, power-loss and brownout behaviors, partition tolerance.
– Why: sites fail in messy ways; you must plan to keep operating safely.
– Starter outcomes: HA patterns per site tier, chaos drills (safe scope), recovery time goals, cold/warm start guides. - Security, Identity & Supply Chain
– What: device/host identity and attestation, SBOM/VEX handling, signed artifacts, sealed secrets, secure update channels.
– Why: edge sprawl increases attack surface; prevention beats incident response.
– Starter outcomes: minimum viable hardening baselines, rotation periods, break-glass procedures, and tamper evidence. - Observability & Remote Ops
– What: metrics/logs/traces across nodes, apps, networks, and models; fleet health dashboards; remote remediation playbooks.
– Why: you can’t fix what you can’t see—especially across 1,000+ sites.
– Starter outcomes: golden signals, SLOs, runbook links from alerts, and ticket/webhook integrations. - Accelerators & Workload Classes
– What: CPU/GPU/NPU/DSP profiles; video/vision pipelines; time-series analytics; real-time/near-real-time workloads.
– Why: right-sizing hardware and models drives performance and cost.
– Starter outcomes: sizing matrices, thermal/energy envelopes, and model-to-hardware mapping.
Reference Architecture
- Device & Field Layer: sensors/PLCs/RTUs, cameras, meters, gateways; hardware-backed identity where feasible.
- Connectivity: segmented L2/L3, Wi-Fi/private 5G, TSN (when required), SD-WAN; inline enforcement and visibility taps.
- Edge Compute: lightweight orchestration, signed containers/WASM/micro-VMs, protocol adapters, time-sync, buffering/quality gates, offline-first.
- Data Services: local time-series/event stores, object cache, schema/semantic alignment, compression, sync to central.
- Integrations & Apps: CV/analytics/ML at edge, control apps, site dashboards, and APIs to enterprise systems (MES / CMMS / BMS /EMS /WMS /TMS / EHR as applicable).
- Governance & Safety: policy-as-code (who can act, on what, when), RBAC/ABAC, HITL approvals for sensitive actions, rollback, evidence capture, audit trails.
Deliverables
- Reference Architectures with design rules and BOM considerations.
- Evidence Packs (policy → control → artifacts; approvals, logs, hashes).
- Masterclasses (edge orchestration, data plane, networking, resilience, governance).
Cadence & Calendar
- Quarterly showcase (2–3 hours): cross-site demos and outcomes.
- Annual anchors: aligned to IoT Slam; deep dives, and masterclasses.
Participation Levels
- Member: attend, learn, and provide feedback.
- Contributor: bring use cases, share artifacts, review drafts, join a workstream.
- Workstream Lead: drive deliverables to closure and present outcomes.
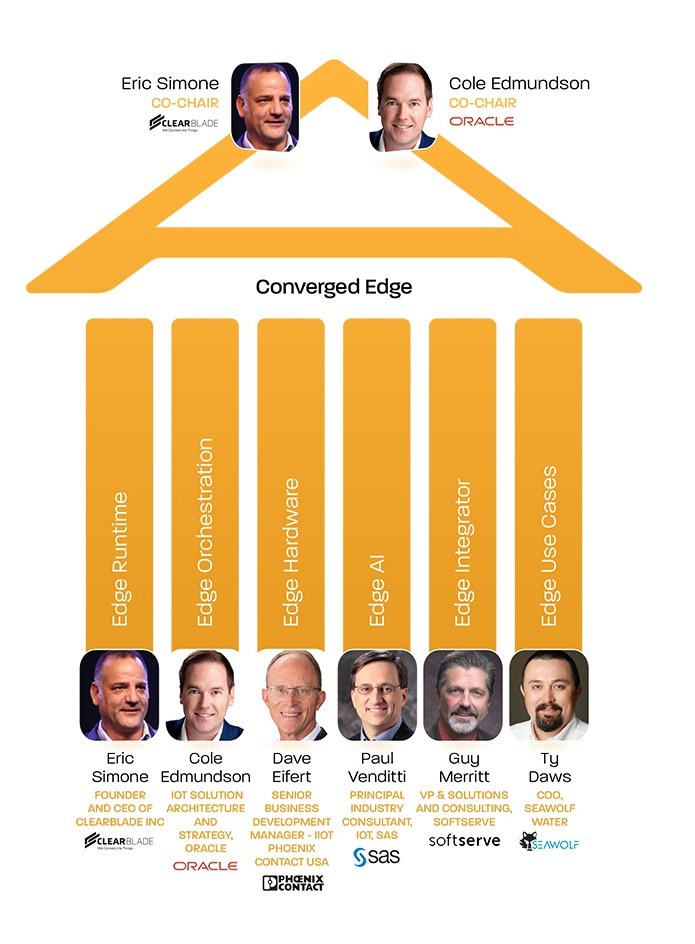
- Chair/Steering: set direction, resolve blockers, uphold governance/quality bars.
How to Get Involved
- Join the CECoE and select a workstream: https://iotcommunity.net/join-us/
- Sponsor a workstream or propose a pilot: sponsors [at] iotcommunity [dot] net
The IoT Community® Converged Edge CoE helps practitioners run real-world workloads at the edge—reliably, securely, and at scale. We connect platform teams, operators, and partners to deliver measurable outcomes—grounded in governance, evidence, and a community that ships.