IoT Security, Safety & Resilience Center of Excellence
Protect, detect, recover—without downtime.
Executive Summary
The IoT Security CoE is a practitioner-led forum focused on securing connected devices, edge platforms, and operational environments—without breaking safety or availability. We publish reference architectures, playbooks, evaluation suites, and audit-ready evidence so organizations can harden IoT/OT estates, govern software supply chains, manage identity at scale, detect/respond to incidents, and recover fast. The core principle: security is only “done” when it is operable by the people who run sites and fleets every day.
Who We Serve
- OT/IT & Platform Teams: security architects, SOC/OT-SOC analysts, network engineers, edge platform owners, SREs.
- Operations: plant/utilities ops, facilities, clinical/biomed, retail/logistics site leaders responsible for uptime and safety.
- Product & Engineering: device/firmware teams, embedded/software leads, DevSecOps/MLOps owners.
- Risk, Audit & Compliance: CISOs, risk managers, internal audit, safety/compliance leaders.
- Partners: OEMs, integrators/SIs, MSSPs, telecom and cloud providers, standards bodies, academia.
Charter & Objectives
- Know Your Estate: complete, live inventory of devices, firmware, certs/keys, and critical data flows.
- Prevent What You Can: hardening, segmentation, identity/attestation, secure update pipelines, and least privilege.
- Detect What You Miss: OT-aware monitoring, anomaly detection, model/data integrity checks, and threat-led testing.
- Respond Safely: playbooks that contain and eradicate without jeopardizing human safety or critical operations.
- Recover & Learn: validated backups, rapid restore, forensics, post-incident improvements, and audit evidence.
- Prove It: policy-to-control mappings, change records, SBOM/VEX handling, and regulator/auditor-ready artifacts.
Scope
Asset discovery/inventory, device/firmware security, PKI and machine identity, network segmentation and zero-trust access, secure software supply chain and updates/OTA, vulnerability and exposure management (incl. SBOM/VEX intake), OT/IoT monitoring and detections, incident response, backup/restore, safety interlocks, and governance/evidence.
Focus Pillars
- Identity, Attestation & Access
– What: device and service identity at scale (certs/eSIM/iSIM), mTLS, policy-based access (RBAC/ABAC), just-in-time credentials.
– Starter outcomes: per-device credentials, cert rotation runbooks, machine-to-machine access lists with expiries. - Network Segmentation & Zero-Trust Edges
– What: L2/L3 zones, micro-segmentation, policy-based routing, jump-host/SASE for remote ops, private cellular/Wi-Fi roles.
– Starter outcomes: reference zone models, enforcement points, approved change windows, and rollback procedures. - Secure Update & Software Supply Chain
– What: signed artifacts, SBOM ingestion, VEX-aware prioritization, staged rollout/canary with health checks, firmware provenance.
– Starter outcomes: update SLAs by criticality, attested images, blocked unsigned code, reproducible builds. - Detection & OT-Aware Monitoring
– What: protocol-aware sensors (Modbus/OPC UA/MQTT/etc.), baseline behaviors, model/data-integrity signals, threat intel hooks.
– Starter outcomes: golden-signal dashboards, alert→runbook links, suppression hygiene to reduce fatigue. - Resilience, Backup/Restore & Recovery
– What: immutable backups, offline/clean rooms, key escrow, rapid rebuild of gateways/edges, and brownout/break-glass paths.
– Starter outcomes: restore drills passed, recovery time goals documented, evidence bundles preserved.
Reference Architecture
- Device & Field Layer: hardware roots where possible, secure boot, measured boot/attestation, minimal services, tamper evidence.
- Connectivity: segmented VLAN/VRF/SD-WAN/private cellular; policy enforcement points; time-sync; observability taps.
- Edge Compute: signed containers/WASM/micro-VMs; secret management; least-privileged services; offline-first with safe degradation.
- Data Plane: encrypted in transit/at rest; lineage/custody; retention; integrity checks; evidence-first logging.
- Control & SecOps: SBOM/VEX pipelines, vulnerability mgmt, update orchestration, SOC/OT-SOC with runbooks and ticket/webhook links.
- Governance & Safety: policy-as-code (who can act, on what, when), approvals, change control, HITL checkpoints, rollback, and audit trails.
Deliverables
- Reference Architectures with design rules and BOM considerations.
- Evidence Packs (policy → control → artifacts; approvals, logs, hashes/signatures, test results).
- Masterclasses (PKI/identity, segmentation, SBOM/VEX, OT detection, IR for safety-critical estates).
Cadence & Calendar
- Monthly working session (60–90 min): backlog, design reviews, decisions.
- Quarterly showcase (2–3 hours): cross-org demos and outcomes.
- Annual anchors: aligned to IoT Slam; deep dives, red/purple-team exercises, and tabletop drills.
Participation Levels
- Member: attend, learn, and provide feedback.
- Contributor: bring use cases, share artifacts, review drafts, join a workstream.
- Workstream Lead: drive deliverables to closure and present outcomes.
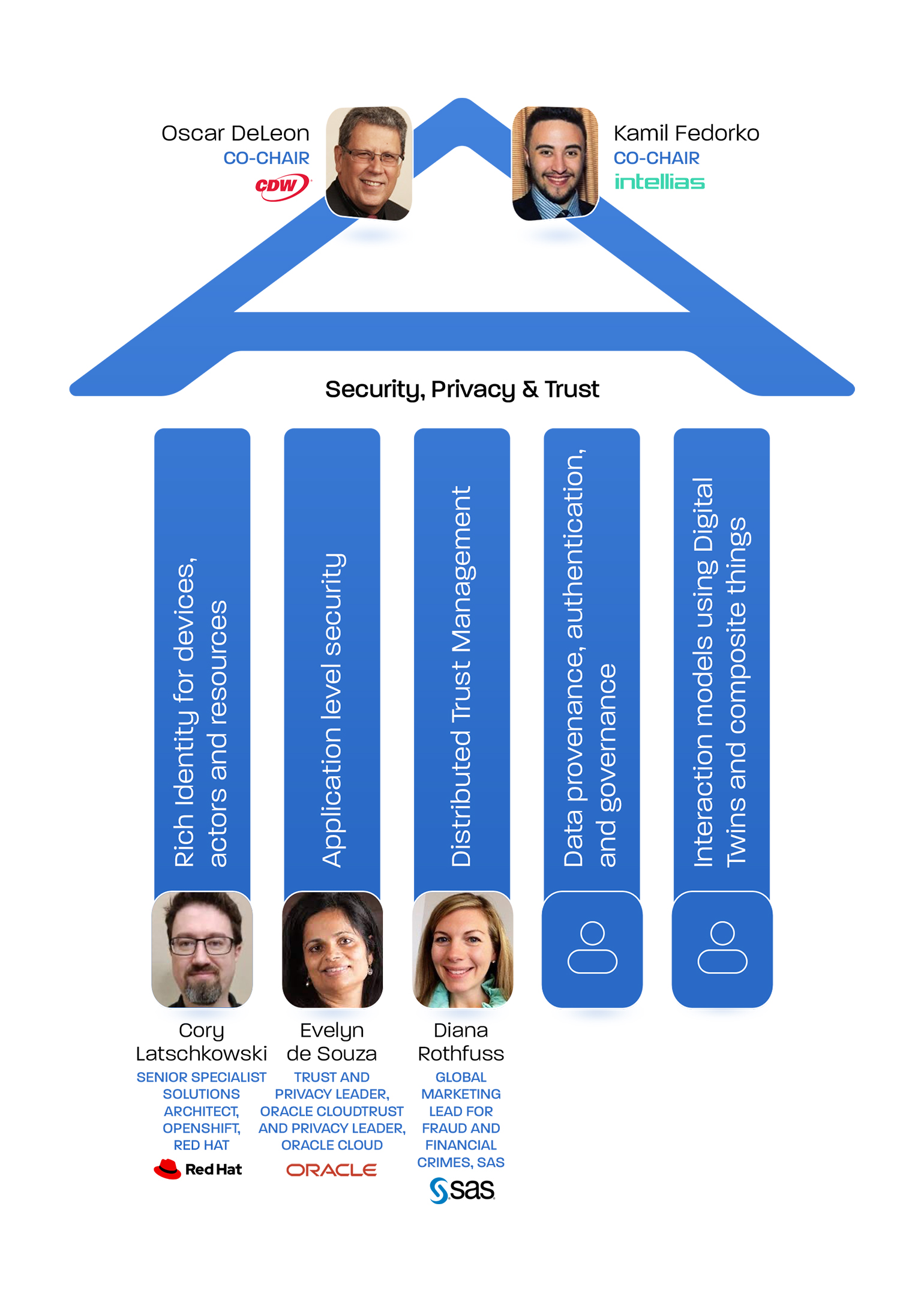
- Chair/Steering: set direction, resolve blockers, uphold governance/quality bars.
How to Get Involved
- Join the Security CoE and select a workstream: https://iotcommunity.net/join-us/
- Sponsor a workstream or propose a pilot: sponsors [at] iotcommunity [dot] net
The IoT Community® Security CoE helps practitioners protect connected operations with patterns they can run. We connect operators, engineers, and security leaders to deliver measurable resilience—grounded in governance, evidence, and a community that ships.